Distributed Denial of Service
When conducting a Distributed Denial of Service attack (abbr. DDoS), a multitude of systems are used for a Denial of Service attack. This scheme is similar to a botnet. In fact, botnets are often used for DDoS attacks, but possess much more abilities.
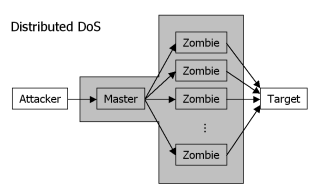
The attacker will exploit known, widespread vulnerabilities to install client software on as many systems as possible. Most of those systems will act as clients (or "zombies"), waiting for the command to begin a DoS attack. One or more systems though will act as masters that know the addresses of the clients and wait for a signal themselves.
When the attack is to begin, the master(s) receive a message containing the target of the attack. They spread the message to the clients, which in turn begin to send packets to the target (depending on the type of the DoS attack).
In order to cover the anonymity of the attacker, communication between attacker, hosts and clients often will use faked source addresses and encrypted communication. Grouping the clients and let different groups attack at different times may help making the attack more efficient. Sometimes schemes common to botnets are also adopted, like organizing the clients in a peer to peer network and using IRC as communication channel.
Common tools for DDos attacks are Trinoo, TFN (Tribal Flood Network), TFN2k and Stacheldraht. On a small feature list of these programs see Distributed Denial of Service Attacks under Remote Control.