NAT Traversal
Note: work in progress
Overview
NAT (Network Address Translation) is widely used to connect private networks to the internet. The main idea is to map several private IP addresses to only one public IP address. Having in mind that P2P network clients should be able to communicate with each other, one basic question comes into mind: how can internet hosts communicate with a host in a private network? We will first have a look at NAT itself and problems it brings. Then, we show how to traverse NATs by either changing router's configuration or by using other tricks.
Network Address Translation
A network address is simply the IP address ( + Port number for UDP/TCP). A NAT router receives an incoming IP packet, saves the address in its NAT table, rewrites sender address to one of its public addresses and sends the packet to the destination address. Now, the NAT router accepts incoming packets on this public address (NAT endpoint). These packets are forwarded to the private host. The most important facts are:
- The mapping depends on the sender's port number. If the private host uses two different outgoing port numbers, the NAT endpoints will differ.
- The private host has to send first. Otherwise no incoming packets will be forwarded to the private host.
- The client does not know all that...
The behavior of the NAT router is not standardized. The only thing that works with every NAT router is simple request and answer. That means the remote host answers a request using the port number the client used for its request. Some NATs allow replies from other ports or even hosts, some use different endpoint mappings for every session.
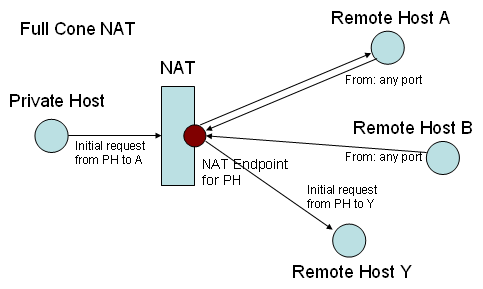
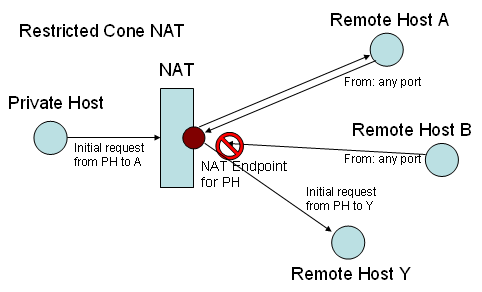
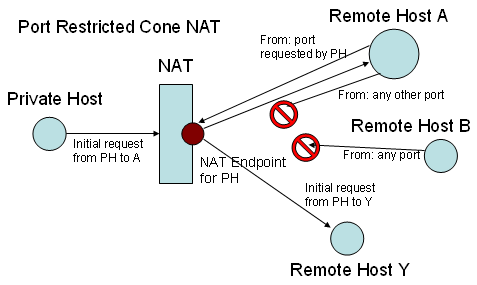
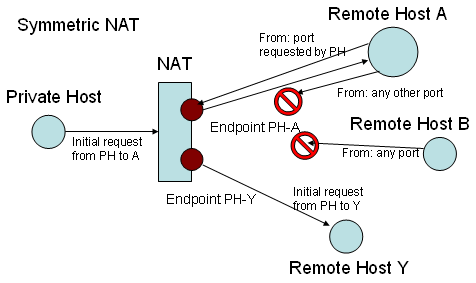
According to their behavior, NATs can be classified into four types:
- Full Cone
- Restricted Cone
- Port Restricted Cone
- Symmetric
router configuration
Port forwarding
UPnP
STUN
TURN
Hole punching
Hole punching deals with the problem two clients behind NAT routers have when they want to establish direct connections. Here, a client A cannot establish a connection with client B, because B is behind a NAT and vice versa. However, using a slightly modified STUN server enables both clients to obtain the public NAT endpoint addresses and the clients' private addresses.
Now hole punching can be tried: both clients send messages to one another. Now, the following happens: client A's message is the first one. It will be rejected or dropped at B's NAT. Hence, A's NAT opened a public endpoint for A's connection. Now, B sends his message. This message will be forwarded by A's NAT. As a result, both NATs have open endpoints; direct communication is established.
One special case is when A and B send their messages synchronously. Here, both messages will reach their targets.
The watchful reader already noticed: What about Symmetric NAT? That's the problem case hole punching cannot handle. We require public endpoint addresses obtained by STUN; so here is the failure. Symmetric NAT assigns different endpoints to different communication partners, so attempts connection from other servers than the STUN server automatically fail.
(picture hole punching to the right)