Distributed Denial of Service: Difference between revisions
No edit summary |
No edit summary |
||
| Line 1: | Line 1: | ||
[this is just a test page and subject to change] |
|||
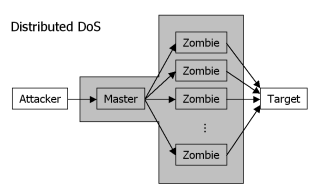
[[Image:Ddos.png|thumb|right|scheme of a DDoS attack]] |
[[Image:Ddos.png|thumb|right|scheme of a DDoS attack]] |
||
When conducting a '''Distributed Denial of Service''' attack (abbr. DDoS), a multitude of systems are used for a [[Denial of Service]] attack. This scheme is similar to a [[Botnet|botnet]]. In fact, botnets are often used for DDoS attacks, but possess much more abilities. |
|||
The attacker will exploit known, widespread vulnerabilities to install client software on as many systems as possible. Most of those systems will act as ''clients'' (or "zombies"), waiting for the command to begin a [[DoS]] attack. One or more systems though will act as ''masters'' that know the addresses of the ''clients'' and wait for a signal themselves. |
|||
When the attack is to begin, the ''master(s)'' receive a message containing the target of the attack. They spread the message to the clients, which in turn begin to send packets to the target (depending on the type of the DoS attack). |
|||
Use fake source addresses and encrypted communication channels |
|||
Revision as of 17:29, 14 November 2004
When conducting a Distributed Denial of Service attack (abbr. DDoS), a multitude of systems are used for a Denial of Service attack. This scheme is similar to a botnet. In fact, botnets are often used for DDoS attacks, but possess much more abilities.
The attacker will exploit known, widespread vulnerabilities to install client software on as many systems as possible. Most of those systems will act as clients (or "zombies"), waiting for the command to begin a DoS attack. One or more systems though will act as masters that know the addresses of the clients and wait for a signal themselves.
When the attack is to begin, the master(s) receive a message containing the target of the attack. They spread the message to the clients, which in turn begin to send packets to the target (depending on the type of the DoS attack).
Use fake source addresses and encrypted communication channels